As the foundation of a vehicle, the chassis provides the framework upon which the rest of a car or truck is built. In addition to acting as the foundation onto which the vehicle's heaviest and most important parts are attached, the chassis also provides crucial structural integrity which prevents the car from collapsing under the strain of its own weight or external forces. So important is the chassis to the vehicle that is mounted on it that if it becomes structurally unsound, it may turn into a performance laggard and a safety disaster waiting to happen.
Thus, automotive assembly giants spend a great deal of money, time, effort and expertise on developing the chassis that will serve their models dependably for years to come.
Connected car cyber security must be approached in the same manner and viewed as the crucial digital structural foundation for vehicle's data and the passenger's safety.
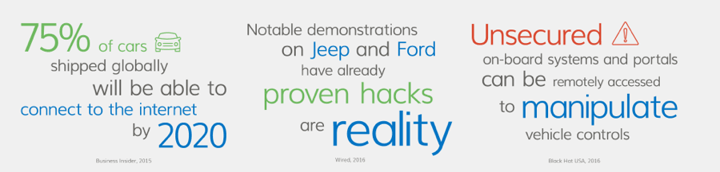
Connected Vehicles as Cyber Targets
Today, vehicles have become large networks on wheels. How so?
It’s all about the three C’s: complexity, connectivity and content. We are currently witnessing a rapid increase in the digital complexity of vehicles:
- The lines of code (software) in a typical vehicle now surpass 100 million compared to 8 million for an F-35 fighter jet
- Electronic Control Units (ECUs or automotive computers) continue to proliferate to more than 100 in popular models and 150+ in high-end vehicles
- There can be as many as seven networks in a typical vehicle
The connectivity of vehicles, especially with the Internet, has dramatically extended their communication reach both incoming and outgoing. Cars and trucks now talk with street signs and cellular phone networks, and download infotainment on demand.
The connected car hordes content like a personal computer on steroids. It collects and communicates vast volumes of information at a rate of more than 25GB per hour. Among all this content is megabytes of personally identifiable information (PII) and other confidential data that are increasingly stored and collected within the vehicle and communicated externally.
Because of the three C’s, the attack surface--the potential target points that delight hackers—of the connected car is growing at such a pace that automotive software apps operating in the vehicle are now subject to similar types of threats that disrupt home and business computers and networks.
Cyber-Security Must be Integral like a Digital Chassis
Today, myriad software vendors, including OEMs, Tier 1s, and 3rd parties, are quite busy developing and integrating applications that are designed to add functionality to the connected car. The potential of the new capabilities in terms of performance, convenience and safety is awesome. But each and every one of these apps can be a target for enterprising hackers. One security hole and they gain access to your car!
To make sure that all the apps are secure, they are tested stringently for resilience against all currently known cyber threats. Upon passing the tests for connected car cyber security defense, they are certified for download into vehicles.
But the automotive cyber-threat landscape is ever-changing. As new threats are discovered (hundreds every day) they are added to the battery of tests and, hopefully, the apps are strengthened further. Then, manufacturers have to worry about how to get the updates to the vehicles already on the road. It’s a never-ending battle.
This approach is backwards.
We need to view automotive cyber security as the digital chassis of the connected car. It is the foundation upon which all of the apps depend, whether for safety, performance or convenience.
Trying to secure thousands of software apps that provide services and data to the connected car is like fitting the chassis after the rest of the car is already designed and built. It’s as if you have already determined the dimensions of the vehicle, the engine size and weight, the placement of other critical components large and small, the tie bars and weld points, etc. and then you try to fit it all on a chassis you have at hand. When something doesn’t connect properly, weighs too much or protrudes too far, you alter the chassis to make everything fit together.
This is an ad hoc method of connected car cyber security that no vehicle manufacturer would use.
Just as the chassis serves as the foundation of the actual vehicle, proper automotive cyber security solutions and a planned regime must serve as the foundation that protects the vehicle regardless of the app. In fact, it must be long-term app-agnostic resilient to attacks now and in the future.
Just as you don’t first develop the upper vehicle, then make it fit an off-the-shelf chassis, you don’t develop software apps then make them fit the ever-changing cyber security landscape.
To be truly secure from cyberattack, vehicles must adopt a mathematically provable, application-agnostic level of protection, a cyber security regime that locks down the vehicle against current and future attack vectors. That’s how it’s done with highly connected, complex and content-rich fighter jets and that’s how it must be done with terrestrial vehicles as well.
Click here to learn how GuardKnox offers the automotive market a unique, comprehensive cyber-security solution that protects against any type of known and unknown cyberattack now and in the future.







